So people usually search for Free Roblox and Roblox Hack and Generator online etc. In hope to get some free Robux coins. Well, the reality is that all those methods and tricks are fake. So today, we have brought you some great tricks on how to get free Robux for Roblox Hack. Steps to Getting Free Robux and Roblox Hack in 2020.
- Now what did we do here? Well, we made an anonymous function and a for loop. The anonymous function is game.Players.PlayerAdded:connect(function(plr) and what this does is just like what a regular function would do, but a Lot less lines. And also made a new variable plr now the for loop made it to where instead of going throughout the script.
- So you have their name, just use google, bing & yahoo and search wit their name Make use of google dorks, that worth our time Now closely observe the Search Results, and go through the Social Media Accounts with that usernames, if any of the accounts are suspicious to you then, make a note of that profile URL, also if any other info attached to the profile then note them also.
The internet is a dangerous place, replete with shady people looking to steal your personal information. Enabling two-factor authentication (sometimes called two-factor verification) is one of the best way to keep your online accounts secure. However, famed hacker Kevin Mitnick shows how even this security measure can’t completely protect your data if you don’t remain constantly vigilant.
The hack in question was not developed by Mitnick, who works as Chief Hacking Officer for security firm KnowBe4. Credit for that goes to Mitnick’s friend and white hat hacker Kuba Gretzky. The tool is known as evilginx, and it makes phishing feasible even when the target uses two-factor authentication. It’s essentially a man-in-the-middle attack, but it uses proxy_pass and sub_filter to modify and capture HTTP traffic. It requires a Nginx HTTP server and some familiarity with Debian Linux. Many people have the necessary expertise to do it.
You can get a complete technical rundown of evilginx on Gretzky’s site, but Mitnick has a nice, digestible video demo of the tool in action(embedded below). He uses LinkedIn as an example, but it could be used on Google, Facebook, and anything else that uses standard two-factor login. The attack starts in the same way all phishing attacks do — with a cleverly crafted email. You have to convince the target to click on a link that loads your site, which masquerades as the page your target expects. In this case, it’s LinkedIn.
Stealing a username and password like this is simple because they don’t change. A two-factor code changes every few seconds, so taking that from your fake page is pointless. Using evilginx, Mitnick shows how the page captures not the 2FA code but the session cookie. That identifies the user to a site, allowing the attacker to hop onto your account immediately.
Mitnick goes on to show how you can load the session cookie manually via the Chrome developer console, which only takes a few clicks. Then, all you need to do is reload the page, and LinkedIn displays the logged-in session. You don’t need to enter a username, password, or even the 2FA code.
Gretzky has published the code for his 2FA hack on GitHub, so everyone has access to it. That means people could try to use it for phishing purposes, but security researchers and educators can also help protect users. It just goes to show you; even two-factor authentication won’t protect you from your own poor decisions.
Now read: 20 Best Privacy Tips to Stay Anonymous Online
In the spirit of DEF CON and a week of hacking, Tech Talker covers one question he gets asked all the time: How do you 'crack' a password?
I’m going to cover one question that I get asked all the time: How do you 'crack' a password?
To answer that, I’m going to take you through the steps a hacker would use to break your password—so that you can avoid some of the pitfalls that would make you an easy target to any password cracker out there.
What's a Hash?
First, let’s talk about how passwords are stored. If a website or program is storing your password--like Google, Facebook or anywhere that you have an online account--the password is generally stored in the form of a hash. A hash is basically a secure way of storing passwords based upon math.
A hash is also a way of scrambling a password—so if you know the trick, you can easily unscramble it. It would be similar to hiding a key to your house in your front yard: if you knew where the key was, it would take you only a few seconds to find it. However, if you didn’t know where the key was it would probably take you a long time to find it.
The 2 Types of Hacker Attacks
Now, let’s break down password attacks into two different types: online and offline.
Offline attacks are where a hacker can take a password hash, copy it, and take it home with them to work on. Online attacks require the attacker trying to login to your online account to go to the specific website they are targeting.
Online attacks on secure websites are very difficult for a hacker, because these types of sites will limit the number of times an attacker can try a password. This has probably happened to you if you’ve forgotten your password and been locked out of your account. This system is actually designed to protect you from hackers who are trying billions of guesses to figure out your password.
An online attack would be like if you tried to search for someone’s hidden key in their front yard while they were home. If you looked in a few places, it probably wouldn’t look too odd; however, if you spent all day in front of the house, you’d be spotted and told to leave right away!
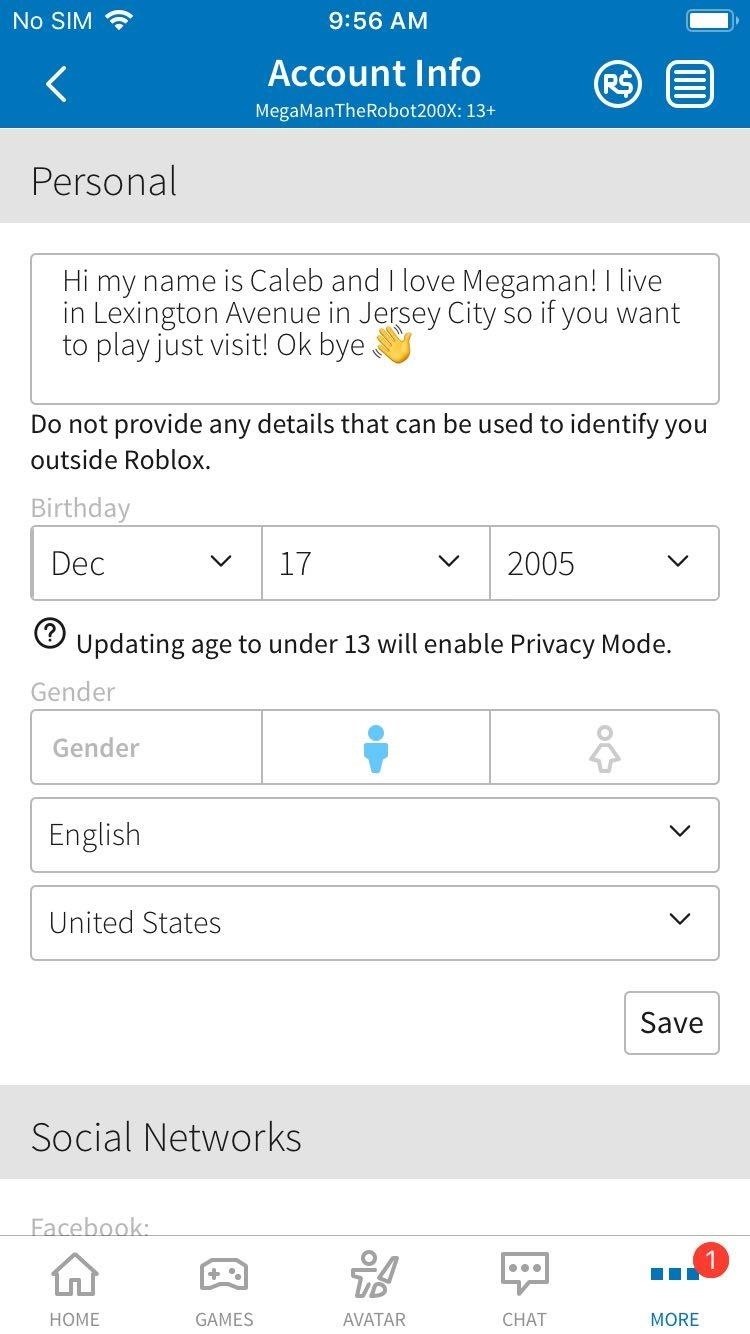
In the case of an online attack, a hacker would most likely do a lot of research on a particular target to see if they could find any identifying information about them, such as children’s names, birthdays, significant others, old addresses, etc. From there, an attacker could try a handful of targeted passwords that would have a higher success rate than just random guesses.
Offline attacks are much more sinister, and don’t offer this protection. Offline attacks take place when an encrypted file, such as a PDF or document, is intercepted, or when a hashed key is transferred (as is the case with WiFi.) If you copy an encrypted file or hashed password, an attacker can take this key home with them and try to crack it at their leisure.
Although this may sound awful, it’s not as bad as you may think. Password hashes are almost always 'one-way functions.' In English, this just means that you can perform a series of scrambles of your password that are next to impossible to reverse. This makes finding a password pretty darn difficult.
Essentially, a hacker has to be very very patient and try thousands, millions, billions, and sometimes even trillions of passwords before they find the right one. There are a few ways hackers go about this to increase the probability that they can find your password. These include:
Dictionary Attacks
Mask/Character Set Attacks
Bruteforce

Let's talk more about each of these.
Dictionary Attacks
Dictionary attacks are just what they sound like: you use the dictionary to find a password. Hackers basically have very large text files that include millions of generic passwords, such as password, iloveyou, 12345, admin, or 123546789. (If I just said your password, change it now!!!)
Hackers will try each of these passwords --which may sound like a lot of work, but it’s not. Hackers use really fast computers (and sometimes even video game graphics cards) in order to try zillions of passwords. As an example, while competing at DEFCON this last week, I used my graphics card to break an offline password, at a speed of 500,000 passwords a second!
Mask/Character Set Attacks
If a hacker can’t guess your password from a dictionary of known passwords, their next option will be to use some general rules to try a lot of combinations of specified characters. This means that instead of trying a list of passwords, a hacker would specify a list of characters to try.
For example, if I knew your password was just numbers, I would tell my program to only try number combinations as passwords. From here, the program would try every combination of numbers until it cracked the password. Hackers can specify a ton of other settings, like minimum and maximum length, how many times to repeat a specific character in a row, and many more. This decreases the amount of work the program would need to do.
So, let's say I had an 8 character password made up of just numbers. Using my graphics card, it would take about 200 seconds--just over 3 minutes--to crack this password. However, if the password included lowercase letters and numbers, the same 8 character password would take about 2 days to decode.
Bruteforce
If an attacker has had no luck with these two methods, they may also 'bruteforce' your password. A bruteforce tries every character combination until it gets the password. Generally, this type of attack is impractical, though--as anything over 10 characters would take millions of years to figure out!
As you can see, cracking a password isn’t as hard as you may think, in theory--you just try trillions of passwords until you get one right! However, it's important to remember that finding that one needle in the haystack is sometimes next to impossible.
Your best safety bet is to have a long password that is unique to you, and to whatever service you’re using. I’d highly recommend checking out my episodes on storing passwords and creating strong passwords for more info.
Comments are closed.